2003
Year of Establishment

100s
of Customers Worldwide

4.9/5
Customer Rating
How Fingent Helps
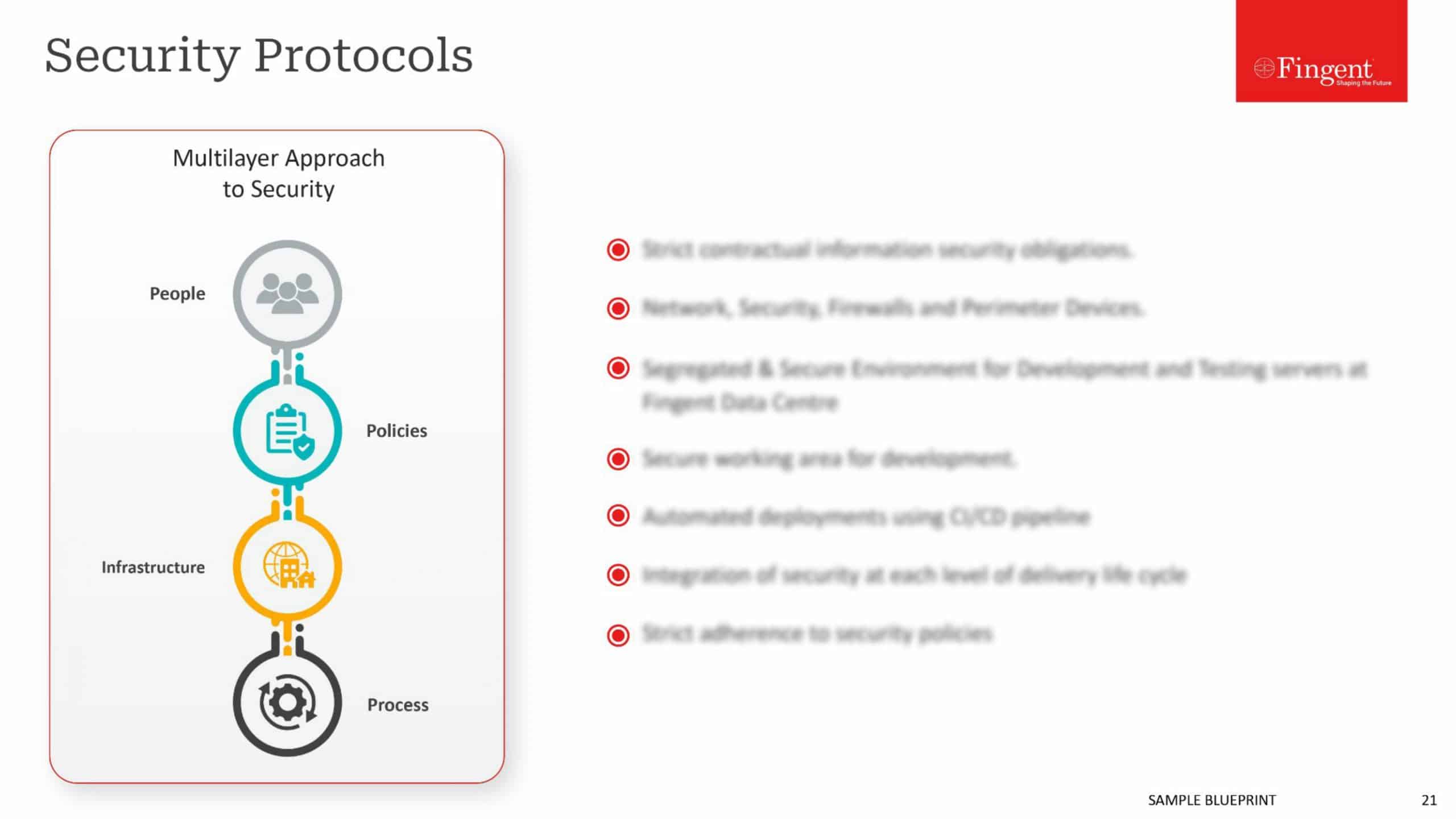
Our security design ensures that your app is secure both internally and externally. We address security-related requirements across each of the three primary domains: application development lifecycle, application development governance, and application runtime hosting.
We realize the importance of your critical applications functioning securely and without interruption. This is why we ensure that every application has its own specifically tailored and secured environment. To this effect, we take a cost-efficient and practical cloud-based hosting approach that protects your applications and equips your business against attacks.

Our Application Security Services
Successful Application Security Program
Foolproof Data Security Solutions
Top-Notch Operating and Consulting Services
Accomplished Team of Experts
Successful Application Security Program
Spotting and understanding the vulnerabilities in your coding is only half the battle won. As your security partners, we ensure that your application security program is successful. You can be confident that with our expert technical support and faster remedy turn around we can bring in more application security knowledge into your business.
Foolproof Data Security Solutions
Your data needs to be protected from internal and external breaches. Our data protection technology ensures that critical data of your organization is always protected. Our encryption technologies help you optimize control over your data. Explore
Top-Notch Operating and Consulting Services
If you need help in fortifying your security operations, our skilled consultants can assess your capabilities, build a world-class security operations center and improve your security posture.
Accomplished Team of Experts
With years of experience in assisting clients globally, our team of experts has built up a wealth of knowledge in achieving a successful application security program. They will assist you in introducing, growing and maintaining application security within your organization.
Why innovate your business with us
Consistent high-quality results with robust agile teams and dedicated QA practices
Highly cost-effective and best-of-breed solutions with no last minute surprises
Transparent project management with maximum adherence to deadlines
Our Unique Approach & Process
By initiating your project with Fingent, you get a dedicated and skilled team backing you up round-the-clock. All our processes are customer-oriented, designed to reduce the cost of business operations, address IT resourcing challenges, and offer you a competitive edge. We start with a deep analysis of your requirements and continue our relationship with post-launch support and updates.
1
Research and Discovery
2
Validating and Shaping Idea
3
Design and Prototyping
4
Development
5
Testing and Quality Assurance
6
Maintenance and Support
Contact Us
Hundreds of leading businesses have derived strategic advantages from our transformative solutions.
The entire engagement was completely transparent and very systematic. It’s been an exceptional working experience.
Their team is completely committed to our success as a client, and they do that with their dynamic team.
They’ve also been great at meeting the needs of our timeframe versus theirs.
They go above and beyond what the typical developer interaction would be.
They were highly responsive to our needs.
We found their project management solid.
Reviews from engineers testify that their code was consistently solid and comprehensively documented.
I have been very pleased with Fingent Corporation’s user experience and design capabilities.
Fingent’s project team demonstrated passion and commitment throughout the dev cycle and it was very evident in their work.
They’re an honest company to deal with … they were always fair and reasonable.
FAQs
Application security is the use of hardware, software, and processes to improve the security of a given application. This includes not just finding and fixing vulnerabilities but also preventing any external or internal security breaches.
Hyperconnectivity, IoT and customer demand requires that all businesses use apps. Those apps need to be protected. According to a security report by Veracode, 83% of applications have at least one vulnerability just in the first scan. Besides, hackers look for weak links in operating systems so they can find a chink in the armor and attack your business.
Most often, larger vendors offer both tools and services. It is important to find out from your vendor what their orchestration plan is. If your business requires expanding onto various platforms, find out if they are willing to include those platforms in their suites.
- Static testing – analyzes code at fixed points.
- Dynamic testing – analyzes running code.
- Interactive testing – combines elements of static and dynamic testing.
- Mobile testing – examines how an attacker might leverage mobile apps.
- Encryption and anti-tampering tools
- Threat detection tools
The foremost challenge is to keep up with the ever-evolving security and application development tools market. Another challenge is anticipating your business needs as your application portfolio requirements become increasingly complex. A third challenge is finding the right tool that fits the requirements of different teams within the IT operations.
- SQL injection vulnerability
- Sensitive data exposure when data is transmitted and stored
- Non secured passwords, exposed session IDs in the URL
- Attack on the browser itself
- Accessing a web application resource by just knowing the URL